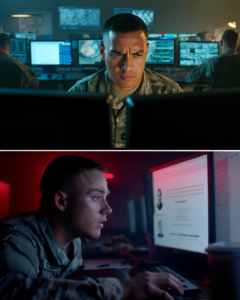
Night fell over Forward Operating Base Sentinel so quickly it seemed to swallow sound itself. Pale yellow lights washed over rows of metal containers, coils of barbed wire, and silent watchtowers. Inside the operations building, everything ran as usual—computers humming, monitors flickering with data, soldiers rotating through their shifts.
Lieutenant Ethan Cole sat in front of his screen, eyes locked on lines of code and access logs. An anomaly had appeared three hours earlier: a packet of data transmitted خارج the system, encrypted at a high level, with no authorization in the schedule.
“We may have a data breach,” he said, his voice low but steady.
Sergeant Miller, the unit’s cybersecurity lead, turned his chair. “Could be a system glitch.”
Ethan shook his head. “No. This was intentional access. Someone pulled mission data.”
The room shifted. Sentinel was supposed to be “secure”—a logistics command hub where plans were coordinated before deployment. If information here was compromised, the consequences would spread far beyond the base.
“Who do you suspect?” Miller asked.
Ethan paused. “Anyone with level-three clearance or higher.”
The list wasn’t long—and every name on it belonged to his team.
The search began that very night.
Ethan moved from section to section, reviewing cameras, access logs, cross-checking timestamps. Everything pointed to one thing: no signs of external intrusion. No unknown personnel. No alarms.
Only one possibility remained.
An insider.
He hated the word. It carried the weight of betrayal, shattering the fragile trust between soldiers who lived side by side.
He started with Corporal Reyes, the data analyst. She worked in a small room, blue monitor light reflecting off her tense face.
“Reyes, I need to check your account,” Ethan said.
She nodded immediately. “What’s going on, sir?”
“Data leak.”
She stepped aside. Ethan checked—clean. No anomalies.
Next was Lieutenant Harris, logistics. Then the comms chief. Then the systems tech. One by one.
All clean.
But the data had still been sent.
Time passed. 0200 hours.
Miller returned with an update. “I traced the transmission. The packet originated from the main ops room… from a personal terminal.”
Ethan looked straight at him. “Whose?”
Miller hesitated. “We need to verify—”
“Whose?” Ethan repeated.
Miller exhaled. “Yours.”
The room seemed to freeze.
Ethan said nothing. He turned back to his screen, pulling up his access logs. The timeline was clear: 23:17—login under his credentials. 23:19—mission files accessed. 23:22—data transmitted.
“That’s impossible,” Ethan said. “I was in the briefing room.”
“Cameras confirm,” Miller replied. “You left at 23:25.”
Ethan clenched his fists. “Then someone used my account.”
“Or…” Miller didn’t finish.
“No,” Ethan cut him off. “I didn’t do this.”
But the data didn’t lie.
Suspicion crept into every glance. Soldiers who once trusted him now kept their distance. No one said it outright—but Ethan felt it.
He had become the prime suspect in his own base.
“We need to suspend your access,” Miller said hours later. “Procedure.”
Ethan nodded. “Do it.”
He didn’t argue. But beneath the surface, something darker stirred—not just concern, but a deep, gnawing confusion.
If it wasn’t him… then who?
And how?
He went back through every detail. Time, location, habits. Something didn’t add up.
23:17—login.
He clearly remembered being in the briefing room. Three officers could confirm it.
But the system said otherwise.
Ethan pulled the hallway camera leading to the ops room. He rewound the footage.
23:15—empty.
23:16—a figure appeared.
Head down. Cap low. Face obscured. But the gait…
Familiar.
Ethan froze the frame, zooming in.
A small detail—the way the hand touched the door. A habit he’d repeated hundreds of times.
It looked like him.
Too much like him.
“Someone’s impersonating me,” Ethan told Miller.
“You think?”
“Not think. I’m close to certain.”
“But how would they get your biometric access?”
The question hung in the air.
Then a memory surfaced.
Two weeks earlier—a security upgrade. A technical team had come in to update biometric systems. They had scanned every senior officer.
Including him.
“We need that team’s roster,” Ethan said.
Miller pulled it up.
Minutes later, he looked back, tense. “We have a problem.”
“What?”
“There’s no record of any technical team that day.”
Ethan felt a chill run down his spine.
“Meaning…?”
“Either the records were wiped. Or…” Miller swallowed. “They were never authorized.”
The truth began to take shape.
Someone had infiltrated the base—not with force, but with trust. They posed as technicians, harvested biometric data, and waited.
And they chose Ethan as the perfect cover.
But why?
Ethan checked what had been stolen.
Not current operations.
A future mission. Classified. Sensitive.
If that fell into enemy hands…
“We’re out of time,” Ethan said. “They’ll move soon.”
“We report this,” Miller replied.
Ethan shook his head. “If we do, the mission gets scrapped—and whoever’s behind this disappears.”
“Then what?”
Ethan’s eyes hardened. “We use me as bait.”
The plan was simple—and dangerous.
They would let the rumor spread: Ethan was the insider. Controlled, deliberate. If the real culprit was watching, he’d be forced to act.
Ethan would become the target.
The next night, the base remained quiet. But beneath it, a trap was set.
Ethan sat alone in the ops room, access restricted, pretending to cover his tracks.
00:12.
A signal flickered—unauthorized access attempt… using his credentials.
“Got him,” Miller whispered over comms.
Ethan didn’t turn. He waited.
The door opened softly.
Footsteps.
“Stop,” Ethan said without looking back. “I know you’re there.”
No response.
Ethan stood and turned.
The man stepped into the dim light.
Ethan froze.
It was… him.
Not a reflection. Not a trick.
Another man—nearly identical.
“Good evening, Lieutenant,” the stranger said calmly.
“Who are you?” Ethan asked.
“A convenient version of you.”
In that moment, everything clicked.
Not just data theft.
Replacement.
“What’s the plan?” Ethan asked.
“Simple,” the man replied. “You’re exposed as a traitor. I take your place. No one questions it.”
Ethan gave a faint smile. “You underestimate my team.”
“No,” the man said. “I understand systems. People trust data more than people.”
A beat.
Then Ethan tilted his head slightly. “Here’s what you missed.”
“What?”
“You’re not the only one being watched.”
Lights snapped on. Doors burst open. Armed soldiers flooded in.
Miller stepped in behind them. “It’s over.”
The imposter didn’t resist. He just looked at Ethan and smiled faintly.
“You win this round,” he said. “But you still don’t know who’s behind it.”
Ethan said nothing.
The man was cuffed and taken away.
Days later, the base returned to routine.
Reports were filed. The compromised mission adjusted. The threat contained.
Ethan stood alone on a watchtower, staring out over the endless desert.
Miller joined him. “You okay?”
Ethan nodded. “Yeah.”
“We still don’t know who’s behind it.”
Silence.
“Maybe we never will,” Ethan said.
“You think so?”
Ethan looked out into the distance. “In war, the most dangerous enemy isn’t the one you can see.”
Miller didn’t reply.
The wind carried sand across the base.
And this time, Ethan knew one thing for certain:
Even in a place called “secure”…
Nothing ever truly is.
News
Betrayed in the line of duty: The soldier stayed alone in the ambush to save his comrades
The night wind sliced through the shattered concrete walls like thin blades. The city of Al-Hadar lay in darkness, lit…
MEGHAN MARKLE DROPS THE ‘SECRET’ TO A LASTING MARRIAGE: A POWERFUL PIECE OF ADVICE THAT LEFT THE BRIDE-TO-BE IN THOUGHT!
Meghan Markle pictured in Australia this month (Image: GETTY) Meghan Markle appeared to offer some helpful advice to a bride-to-be in a…
A once-in-a-lifetime opportunity for Prince William and Harry to reunite after years of estrangement
The royal brothers could meet again in June (Image: Getty) Prince William and Prince Harry could be reuinited at a royal wedding in…
WRONG TIMING, WRONG MOVE: IS HARRY FURTHER ISOLATING HIMSELF FROM THE FAMILY?
Prince Harry recently visited Ukraine (Image: Getty) Prince Harry’s recent surprise trip to Ukraine is indicative of the Prince of Sussex’s behaviour, an…
CARDI B ‘AIRS HER OWN DIRTY LAUNDRY’: ADMITS TO LACK OF NEW MUSIC AND DREAMS OF A $14 MILLION PAYDAY IN JUST TWO SHOWS!
While Nicki Minaj fans were busy measuring the Little Miss Drama tour against the Pink Friday 2 run, Cardi B…
OFFSET FIGHTS BACK: DENIES PUNCHING SECURITY GUARD, COUNTER-ACCUSES OPPONENT OF DISRESPECTFUL CONDUCT!
Getty Offset claims the security guard suing him for assault provoked the fight that went down at a L.A. weed shop…
End of content
No more pages to load